By Andrea Favalessa, 27 January 2024

Source : Creative Commons, FMT
When discussing fifth-generation wireless technology, commonly known as 5G, most non-experts think exclusively of faster connection speeds. While this is certainly true, it represents only one of the many advancements 5G introduces compared to previous generations of wireless technology (4G, 3G, 2G, and 1G). In fact, 5G is poised to revolutionize multiple industries, bringing groundbreaking upgrades.
Alongside these numerous advancements, however, come potential challenges—particularly in the realm of security. It is therefore crucial to understand these new challenges, the regulatory measures already being taken to address them, and what more can be done to ensure we harness only the positive aspects of 5G. In this report, I have chosen to focus on one specific area: the Internet of Things (IoT)1 and the challenges it introduces to the 5G network. The rationale for this focus is that while much scrutiny has been placed on addressing risks at the software or infrastructure level, less attention has been paid to these simpler yet critical components of the 5G network. Because of this, I believe there is significant room for improvement in enhancing the cyber resilience of the 5G network by addressing IoT-related risks. Before delving into these challenges and possible solutions, it is first necessary to understand what 5G is and the innovations it brings.
What Does 5G Introduce
Addressing all aspects introduced by 5G would warrant an entire academic essay; therefore, I will focus briefly on some of its main innovations, the ones I deem more relevant for this article. 5G represents an evolutionary necessity to accommodate emerging technologies that demand more advanced capabilities, for which 4G standards are no longer sufficient. Specifically, 5G is designed to meet three primary use cases:
- eMBB (enhanced Mobile Broadband): This feature provides high-speed broadband services, elevating connection speeds to unprecedented levels (Mohan, 2022). Use cases include virtual reality, augmented reality, and 4K/8K streaming, which require high-speed connectivity and large data throughput.
- mMTC (massive Machine Type Communication): This capability focuses on enabling communication between billions of low-power, low-data-rate devices that need to operate efficiently and reliably over long periods (Ghayas, 2021). It forms the backbone of smart cities, allowing billions of new IoT devices to connect to the network.
- URLLC (Ultra-Reliable Low Latency Communication): Designed for services requiring extremely low latency and high reliability (Mohan, 2022). Examples include remote medical operations and autonomous vehicles, where even a slight delay in response could have serious consequences.
Two key innovations in the structure of the 5G network enable these three use cases to function effectively: network slicing and MEC (Multi-access Edge Computing).
Network Slicing and Multi-Access Edge Computing
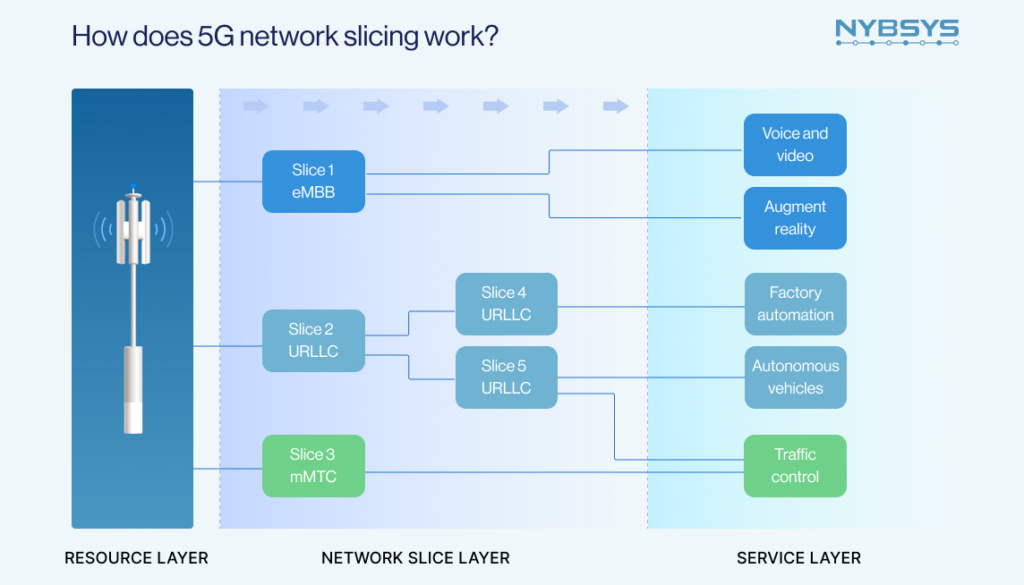
On the one hand, network slicing allows a shared physical network infrastructure to host multiple virtual networks, managed through the software2 (O’Malley, 2024). These virtual networks referred to as slices, are tailored for specific use cases, such as, one slice for autonomous vehicles leveraging URLLC and another for media streaming using eMBB. By doing so, network slicing maximizes efficiency for each individual use case while eliminating the need for separate networks for each application.
Source : NYBSYS
The advantages of network slicing are multifaceted. It enhances efficiency by allowing for better allocation of resources based on actual demand, thereby reducing resource wastage (O’Malley, 2024). Furthermore, it allows greater scalability thanks to the virtualization process, which enables slices to be created, modified, or deleted rapidly in response to changing demands (ibid). In addition, network slicing significantly improves security by isolating virtual network segments from one another, which reduces the risk of cross-network breaches and facilitates the implementation of customized security measures for each use case (Nile Secure).
On the other hand, MEC addresses the challenges posed by increased data flow and the growing number of devices by extending cloud computing capabilities closer to the edge of the network. By processing data locally, it minimizes latency, improving performance for real-time applications, such as autonomous vehicles and remote healthcare, and reducing congestion by offloading traffic from the core network (Rajamani, 2024). Additionally, MEC enhances security by minimizing the exposure of sensitive information during transmission to a centralized cloud server, enabling localized threat detection, and providing faster responses to potential risks (Gieske, 2024).
Security Risks of IoT Devices in 5G Networks
The benefits of 5G in terms of efficiency are undeniable, showcasing its potential to enhance productivity and innovation. Instead, on the security side, while 5G offers significant improvements thanks to features like network slicing and MEC, it also introduces new challenges (Pernik et al., 2021). The restructuring of the network’s architecture and the significant increase in connected devices create new attack vectors and entry points for malicious actors. Particularly, IoT devices are extremely vulnerable as most lack robust built-in security measures because, compared to infrastructure or software systems, they receive less scrutiny, making them appealing targets for cyberattacks. The main cybersecurity risks related to the IoT are:
- Attackers Exploiting Network Resources
Cybercriminals can leverage 5G’s higher speeds and lower latency—compared to 4G—which allow them to weaponize compromised IoT devices on a massive scale. Using these devices, they can create botnets, launching more devastating Distributed Denial of Service (DDoS) attacks that overwhelm network resources (Vargas & Tien, 2023). While network slicing can help contain the impact by isolating affected segments and preventing cross-network breaches, there would still be a problem to face for the targeted slice.
- Attackers Exploiting Device Vulnerabilities
Many IoT devices lack basic encryption protocols, leaving their device-specific information—such as model, firmware version, or communication protocols—exposed. This allows attackers to identify vulnerabilities and execute precision attacks tailored to specific devices by exploiting known vulnerabilities (Kaspersky, 2020).
- Attackers Exploiting Long-Term Vulnerabilities
In the industry, it is widely known that IoT devices often lag in receiving updates and security patches. This increases risks as many are used for years without maintenance, leaving them vulnerable to exploitation (SentinelOne, 2024).
- Supply Chain Exploits
The complexity of the 5G supply chain introduces risks at every stage, from design to deployment. Errors or weaknesses in IoT devices during the production process are particularly challenging to detect later on and can create long-term vulnerabilities (Kadena & Rajnai, 2024) This is especially concerning as 5G adoption expands globally, increasing reliance on IoT supply chains.
How Should These Issues be Addressed in the Future?
To mitigate most IoT-related vulnerabilities, regulators could require manufacturers to implement two key measures. First, they should enhance the built-in security features of their products, which would help mitigate risks such as DDoS attacks and encryption-related vulnerabilities. Second, manufacturers should adhere to best practices, including the prompt deployment of patches and the establishment of stricter supply chain controls. However, enforcing these measures presents significant challenges. Compliance entails increased costs, and many manufacturers lack the financial resources or technical expertise to implement these requirements effectively (Kaspersky, 2020). Given the critical need to minimize potential disruptions caused by cyberattacks on 5G networks, and the improbability that manufacturers will voluntarily adopt such practices, a top-down legislative approach is essential to enforce standardized regulations for IoT device security.
In this regard, the EU’s 5G Toolbox is a promising initiative that identifies cybersecurity risks and recommends technical and strategic measures to secure 5G networks (NIS Cooperation Group, 2020). The origin of these regulations at the EU level is beneficial, as national governments are often reluctant to impose additional costs on their manufacturers. This is shown in a 2023 report by the NIS Cooperation Group that revealed that eight member states had yet to initiate legislative processes to implement the Toolbox’s measures for “raising security standards in suppliers’ processes”, a measure that would increase costs for manufacturers (2023). This example illustrates how leaving these matters to the jurisdiction of individual member states could result in inconsistent implementation, potentially creating an unequal playing field where some countries favor their manufacturers by adopting laxer or no standards, disadvantageous to other states’ manufacturers and undermining the principles of the EU single market. Further challenges still exist in the Toolbox:
- The Toolbox is composed of recommendations rather than binding directives, limiting its enforceability. The 2023 report from the NIS Cooperation Group highlights that some states are adopting the suggested measures of the Toolbox while others have not, leaving critical vulnerabilities unaddressed. Partial implementation of measures allows attackers to exploit weak points within the network, jeopardizing 5G infrastructure security across the EU (NIS Cooperation Group, 2023).
- The Toolbox adopts a one-size-fits-all approach, treating IoT devices as a homogeneous category despite their varying uses, complexities, and security requirements. This generalization might result in critical devices being under-secured while imposing unnecessary costs on low-risk devices manufacturers.
- Many measures within the Toolbox implicitly target Chinese companies, such as Huawei and ZTE, due to concerns about potential espionage through backdoors or vulnerabilities strategically implemented in their products. While these precautions align with geopolitical realities, they have caused divisions within member states. Between 2020 and 2023, 14 of the 27 EU member states took no action, despite the Toolbox suggesting so, to address risks related to “high-risk suppliers”3(NIS Cooperation Group, 2023). This shows how excluding Chinese companies from national 5G infrastructure is challenging and problematic for European states.
Proposed Solutions for The Future
- To ensure consistent implementation, the Toolbox should be elevated to the status of a directive, making its measures mandatory for all member states. Such an approach would not be unprecedented in the cyber domain and aligns with existing directives such as NIS24. In fact, the 5G Toolbox could serve as the foundation for a future “NIS3” initiative, creating a comprehensive and cohesive framework for regulating 5G networks and IoT security across the EU. This integration would build on NIS2’s objectives, expanding its scope to include specific measures tailored to 5G networks and IoT device security, ensuring a unified and future-proof regulatory approach. Two key reasons justify this shift:
- Regulating 5G is essential to safeguarding the EU single market, as a cyberattack on a company in one member state could trigger cascading disruptions across multiple companies and countries.
- Uneven standards among member states risk creating an unequal playing field for businesses across the EU, undermining one of the fundamental principles of European cohesion: fair competition among member states’ companies.
Elevating the 5G Toolbox to the status of a directive —and potentially embedding it within a broader NIS3 framework— would directly address both of these issues by mandating the implementation of its proposed measures and ensuring uniformity across the Union.
- While providing directives on how to build secured IoT devices is a necessity. The EU should move away from a generalized approach and introduce tailored security frameworks (within the Toolbox in order to make them mandatory) for different categories of IoT devices, based on their type, use, and function. The wide variety of devices encompassed under the IoT label demands such an approach. For instance, it is reasonable for industrial IoT sensors to adhere to distinct security standards compared to autonomous vehicles. Imposing the same security requirements on both would result in industrial IoT sensors being overly secured, unnecessarily burdening their manufacturers with excessive costs, while autonomous vehicles would be inadequately protected.
- Future regulations should address supply chain vulnerabilities in a broad and neutral manner, rather than explicitly or implicitly targeting specific countries or companies, such as Chinese suppliers. Adopting such a strategy would reduce the perception of unfair market practices from the Chinese perspective, thereby mitigating potential political and economic backlash from Beijing. This neutral approach would also foster greater acceptance of the new regulatory framework among EU member states, particularly those concerned about possible retaliatory measures from China, such as trade bans on European companies, given the significant size of the Chinese market for certain industries. Moreover, de-escalating rhetoric around risks associated with Chinese companies would provide states heavily reliant on Chinese suppliers for 5G infrastructure with the flexibility to diversify their supply chains gradually5, minimizing the risk of immediate economic disruptions. Addressing member states’ concerns regarding both security and economic implications is crucial to ensure broad acceptance of the regulation across the Union, thereby avoiding unnecessary political challenges and facilitating the smooth adoption of the 5G Toolbox as a mandatory framework across the EU.
- The internet of things is a network of physical devices, vehicles, appliances, and other physical objects that are embedded with sensors, software, and network connectivity, allowing them to collect and share data (IBM, 2024). ↩︎
- This is achieved through software-defined networking (SDN) that decouples the control plane (which handles decision-making) from the data plane (which manages traffic routing), enabling network administrators to dynamically manage and optimize network traffic; and network function virtualization (NFV) that uses virtualization to run multiple network functions on a shared hardware, significantly reducing dependency on dedicated physical infrastructure (SDxCentral Studios, 2016)
↩︎ - Indirect reference to Chinese companies.
↩︎ - NIS2 aims primarily to achieve a high common level of cybersecurity across the EU by establishing stricter and more harmonized security requirements.
↩︎ - The adoption of the 5G Toolbox will equip companies with the necessary measures to evaluate whether reliance on Chinese suppliers poses a genuine risk. If such a risk is identified, companies will be able to follow the Toolbox’s guidelines to transition to alternative providers effectively.
↩︎



