Author: L R
-
How does collecting and sharing cyber information (best practices, cyber intelligence, strategies) improve security capabilities ? A lot is at stake for the public and private sector alike in understanding the threat to be able to better anticipate it. Moreover, previous incidents have shown how successful communication and information sharing have been helpful to contain…
-
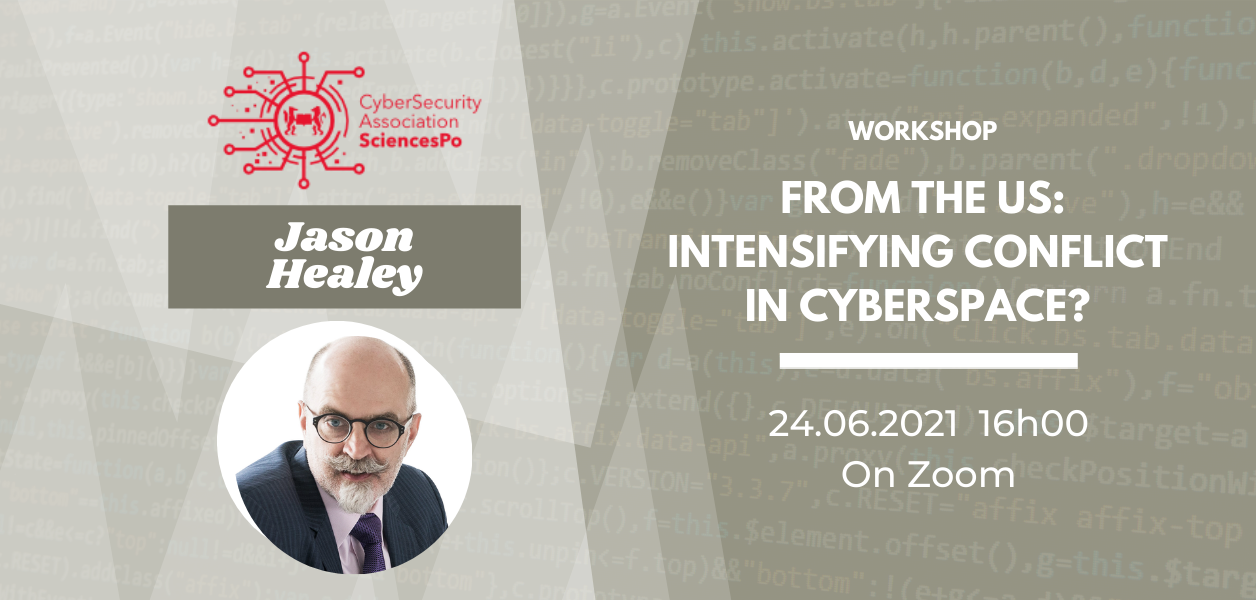
How does the US apprehend cyberspace? What do the concepts of ‘persistent engagement’ and ‘defending forward’ mean? Why has the USA perpetuated intensifying conflict in cyberspace? What are the benefits and disadvantages of the US’s national cyber doctrine? How does that strategy interact with key allies and international norms? How does the NSA conduct mass…
-
Do you know what it means to work in OSINT? Have you always wondered how OSINT relates to cybersecurity? On June 2, the Sciences Po Cybersecurity Association conducted a practical workshop on OSINT techniques used in cybersecurity investigations. The event aimed at providing answers to: How do hackers detect vulnerabilities and prepare for their attacks?…
-
Organisations use cyber threat intelligence (CTI) to understand their threat landscape and make more informed decisions around security. However, what does a CTI organisation actually do? Are you curious to get a sneak peak into what cybersecurity experts do in their daily jobs? On May 27th, SCA hosted another career workshop to discuss the exciting…
-
Pour clôturer cette année, Sciences Po Cybersecurity Student Association a organisé un exercice d’immersion dans une crise cyber. Un petit nombre d’étudiants privilégiés ont donc reçu la mission de représenter l’ANSSI, la DGSE, le Service d’information du gouvernement, le Quai d’Orsay, le Ministère de l’intérieur ou encore celui de la Justice afin de réagir et…